Occasionally we receive support cases from customers performing audits of their Azure AD Audit or Sign in logs and do not know what the service principal \ actor ” Microsoft Approval Management “ is.
After review with Microsoft product engineering teams it was confirmed this is a 1st Party Microsoft Service Principal for the following services and may be logged in customer audit logs during the operation of any of these services in your tenant.
Any of the operations performed by these services such as calculating group memberships, applying group memberships, performing group expirations etc. will be logged in Azure AD audit logs as being performed by “Microsoft Approval Management”. All of the operations performed by these services, are documented in the links above.
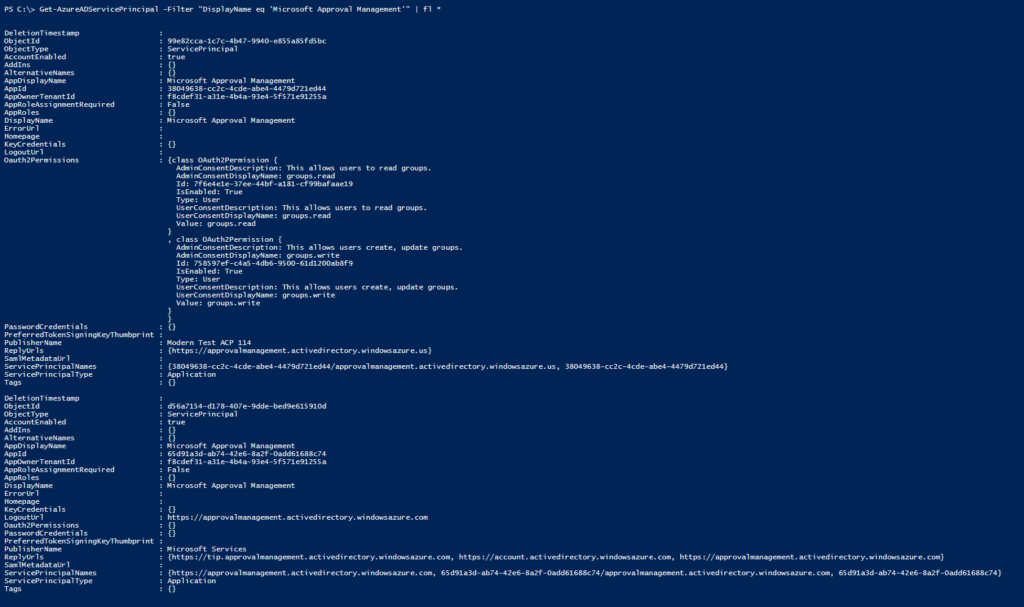
You can confirm this service principal is in your AAD tenant with the AzureADPreview PowerShell module and the following cmd
Get-AzureADServicePrincipal -Filter "DisplayName eq 'Microsoft Approval Management'" | fl *Where you should confirm that the PublisherName = “Microsoft Services” and you may find it listed with the AppID of “65d91a3d-ab74-42e6-8a2f-0add61688c74” or “38049638-cc2c-4cde-abe4-4479d721ed44”
UPDATE:
If this service principal is disabled you may experience strange behavior in the Azure AD Portal when trying to manage groups.
One example, if this service principal has been disabled by the AAD Global Administrator any operation on groups in the AAD portal may return an error : “Unable to complete due to service connection error. Please try again later”
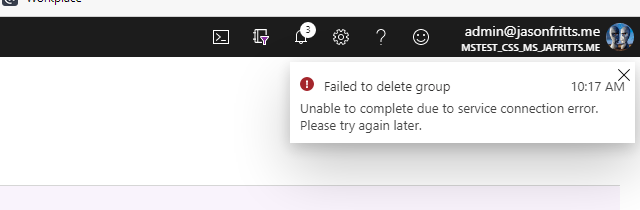
If you receive this error, verify that the Microsoft Approval Management enterprise application has not been disabled.
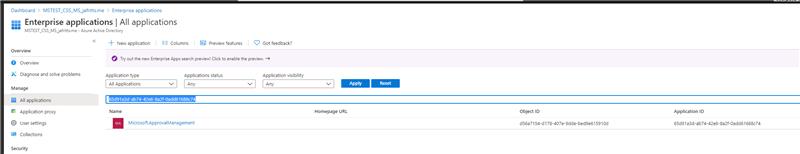
- Go to AAD -> Enterprise Apps blade : Enterprise applications – Microsoft Azure
- Then browse to All applications Set filters to Application type = All Applications, Status = Any, Application Visibility = Any In search box type the appID 65d91a3d-ab74-42e6-8a2f-0add61688c74
3. Open this app’s properties Choose Enabled for users to sign in = Yes Hit Save
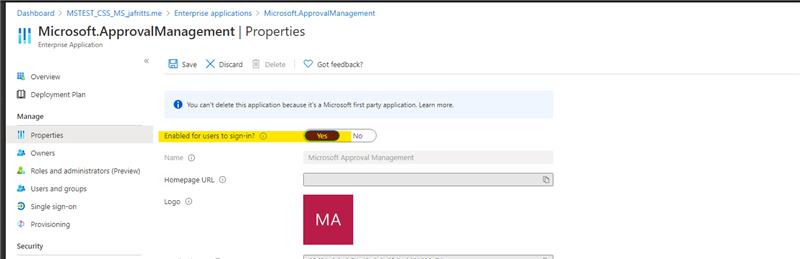
4. Then retry their group operation which failed
NOTE: You may also want to check for app ID 38049638-cc2c-4cde-abe4-4479d721ed44 to verify it is enabled as well.
UPDATE:
If you have other unknown principals showing up in your AAD logs and you would like to verify they are Microsoft 1st party principals please use the Feedback sections of the below articles
Unknown Actors in AAD Audit Reports
Verify first-party Microsoft applications in sign-in reports